Overview
Clion always understands your code and takes care of routines while paying attention to important issues. Instantly navigate to the declaration or context usage of a symbol, search for names, classes, files, or symbols throughout the project, and find your way through a code base with a structured and hierarchical view. For tutorial about how to generate SSH keys, please refer to How to set up SSH keys and connecting to GitHub with SSH. Firstly you need to see whether your server has a public IP address. If yes (I know this is not common), then things are really easy and you can just follow step 1, 2 and 3; otherwise, directly go to step 0, then step 2 and 3.
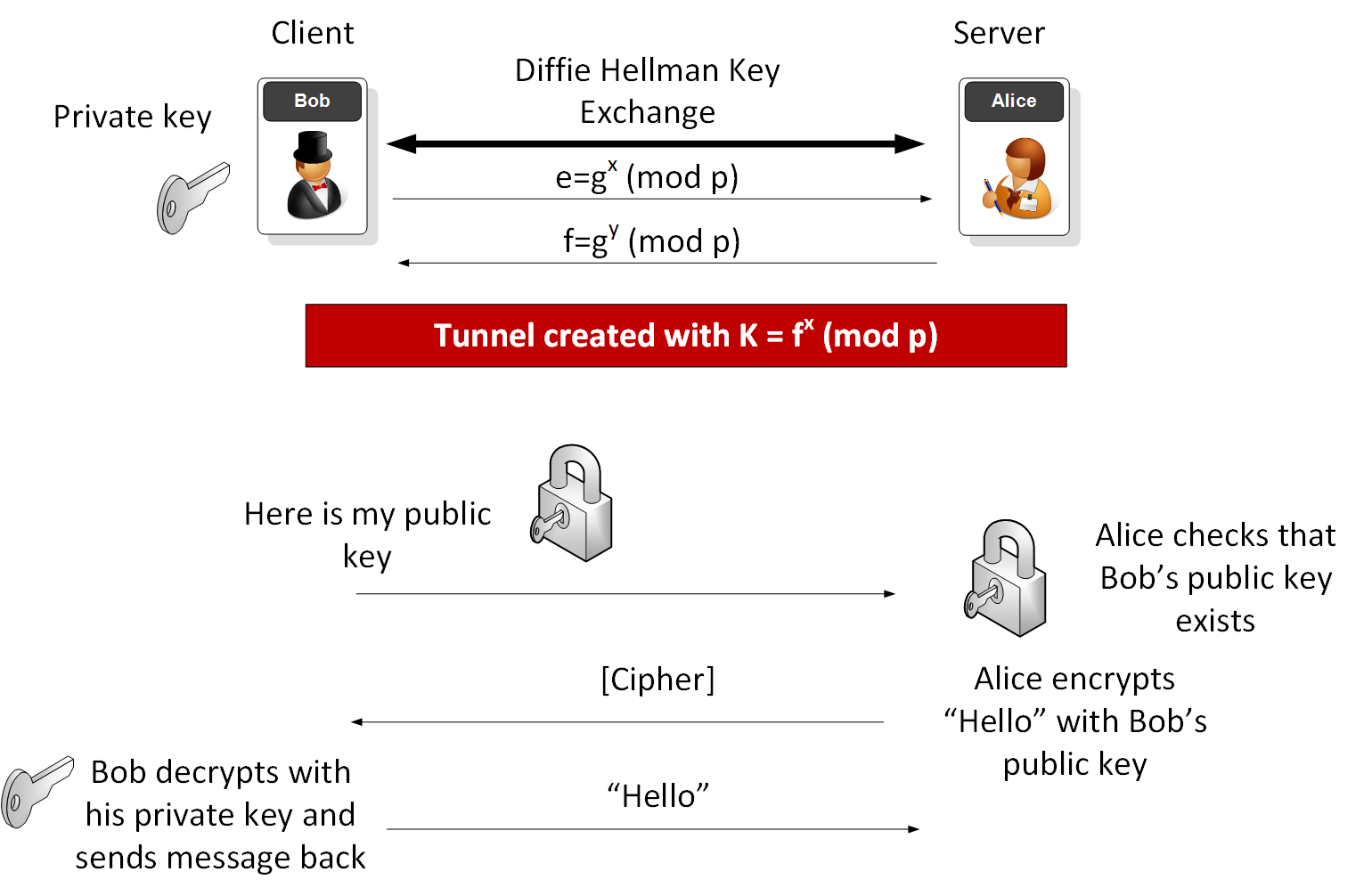
Public key authentication is a way of logging into an SSH/SFTP account using a cryptographic key rather than a password.
If you use very strong SSH/SFTP passwords, your accounts are already safe from brute force attacks. However, using public key authentication provides many benefits when working with multiple developers. For example, with SSH keys you can
- allow multiple developers to log in as the same system user without having to share a single password between them;
- revoke a single developer's access without revoking access by other developers; and
- make it easier for a single developer to log in to many accounts without needing to manage many different passwords.
How Public Key Authentication Works
Keys come in pairs of a public key and a private key. Each key pair is unique, and the two keys work together.
These two keys have a very special and beautiful mathematical property: if you have the private key, you can prove you have it without showing what it is. It's like proving you know a password without having to show someone the password.
Public key authentication works like this:
- Generate a key pair.
- Give someone (or a server) the public key.
- Later, anytime you want to authenticate, the person (or the server) asks you to prove you have the private key that corresponds to the public key.
- You prove you have the private key.
You don't have to do the math or implement the key exchange yourself. The SSH server and client programs take care of this for you.
Generate an SSH Key Pair
You should generate your key pair on your laptop, not on your server. All Mac and Linux systems include a command called ssh-keygen that will generate a new key pair.
If you're using Windows, you can generate the keys on your server. Just remember to copy your keys to your laptop and delete your private key from the server after you've generated it.
To generate an SSH key pair, run the command ssh-keygen.
It will look like this when you run it:
You'll be prompted to choose the location to store the keys. The default location is good unless you already have a key. Press Enter to choose the default location.
Next, you'll be asked to choose a password. Using a password means a password will be required to use the private key. It's a good idea to use a password on your private key.
After you choose a password, your public and private keys will be generated. There will be two different files. The one named id_rsa is your private key. The one named id_rsa.pub is your public key.
You'll also be shown a fingerprint and 'visual fingerprint' of your key. You do not need to save these.
Configure an SSH/SFTP User for Your Key
Method 1: Using ssh-copy-id
Now that you have an SSH key pair, you're ready to configure your app's system user so you can SSH or SFTP in using your private key.
To copy your public key to your server, run the following command. Be sure to replace 'x.x.x.x' with your server's IP address and SYSUSER with the name of the the system user your app belongs to.
Method 2: Manual Configuration
If you don't have the ssh-copy-id command (for example, if you are using Windows), you can instead SSH in to your server and manually create the .ssh/authorized_keys file so it contains your public key.
First, run the following commands to make create the file with the correct permissions.
Next, edit the file .ssh/authorized_keys using your preferred editor. Copy and paste your id_rsa.pub file into the file.
Log In Using Your Private Key
You can now SSH or SFTP into your server using your private key. From the command line, you can use:
If you didn't create your key in the default location, you'll need to specify the location:
If you're using a Windows SSH client, such as PuTTy, look in the configuration settings to specify the path to your private key.
Granting Access to Multiple Keys
The .ssh/authorized_keys file you created above uses a very simple format: it can contain many keys as long as you put one key on each line in the file.
If you have multiple keys (for example, one on each of your laptops) or multiple developers you need to grant access to, just follow the same instructions above using ssh-copy-id or manually editing the file to paste in additional keys, one on each line.
When you're done, the .ssh/authorized_keys file will look something like this (don't copy this, use your own public keys):
Additional Information
Retrieve Your Public Key from Your Private Key
The following command will retrieve the public key from a private key:
This can be useful, for example, if your server provider generated your SSH key for you and you were only able to download the private key portion of the key pair.
Note that you cannot retrieve the private key if you only have the public key.
Correcting Permissions on the .ssh Directory
The instructions in this article will create your server's .ssh directory and .ssh/authorized_keys file with the correct permissions. However, if you've created them yourself and need to fix permissions, you can run the following commands on your server while SSH'd in as your app's system user.
Clion Ssh
Disabling Password Authentication
NOTE: When changing anything about the way SSH is accessed(ports, authentication methods, et cetera), it is very strongly recommended to leave an active root SSH session open until everything is working as intended. This ensures you have a way to revert changes in the event something goes wrongand logins are not working properly.
As an extra security precaution, once you have set up SSH keys, you may wish to disable password authentication entirely. This will mean no users will be able to log into SSH or SFTP without SSH keys. Anyone entering a password will receive a message like:
Or:
Disabling password authentication is an excellent way to improve server security. Please see our guide here for the steps to accomplish this goal.
Then, test whether you're able to log in with a password by opening a new SSH or SFTP session to the server. Passwords should not be able to be used and, if everything has been done correctly, an error will be issued when someone tries to use a password. Unless this setting is changed back to allow password authentication, no users will be able to log in without an SSH key set up.
Remotely editing your work when your server does not have public IP address and you don’t want to spend any money is not so easy. Maybe you can use Team viewer or Anydesk or even chrome remote desktop, but there are high latencies. Maybe you can use ngrok to remotely ssh to your server, you have to use vim and you are not familiar with it at all 😧. I tried to use rmate but it is not convinient to edit across different files in a folder.
I recently found an hot github repository called code-server which is able to run VS Code on a remote server, accessible through the browser. So it suddenly came to my mind that I can remotely edit any code for free as long as I have a linux/macOS environment.
Let’s consider you understand the basic knowledge of SSH key as you are going to use it. For tutorial about how to generate SSH keys, please refer to How to set up SSH keys and connecting to GitHub with SSH.
Firstly you need to see whether your server has a public IP address. If yes (I know this is not common), then things are really easy and you can just follow step 1, 2 and 3; otherwise, directly go to step 0, then step 2 and 3.
Step 1. SSH connect
The -L 8843:localhost:8843 here is local port forwarding which allows you to access local network resources that aren’t exposed to the Internet. The first 8843 is local port, localhost:8843 is the remote code-server default port.
To see whether you can successfully links to the server. The prerequisites are 1) you installed openssh-client 2) you have generated SSH key. If not successfully, maybe you don’t have a public IP address. Then go to step 0.
Step 2. Download code-server

Open this page on your client browser, find the latest release of code-server. Find the binary file for linux and get the downloading address.
Then in the terminal window ssh connected to the remote server, type:
Then your code-server will be installed!
Clion Git Ssh Key
Step 3. Running code-server

Go to the folder of your code waiting to be edited and type code-server in the terminal window ssh connected to remote server.Then open your browser and type localhost:8843, your workspace of VSCode will be revealed to you! The speed is satisfactory to me.
Step 0. Ngrok
Some people will use VPS servers or cloud hosting providers like Vultr, AWS and so on to pay for a public IP address. But here we just need Ngrok, a great tool that can create a tunnel from the public Internet to a port on your local machine. You can give this URL to anyone and any place without the need to pay any money!
Download ngrok onto your remote server and throw the binary file into /usr/local/bin/. Maybe need to sudo chmod a+x ngrok.Then type:
where –region refers to your region. There are four region options: us(Ohio), eu(Frankfurt), ap(Singapore), au(Sydney). If you don’t select a region, the default one is us, which might be slow if you are in Asia.
Then your screen will show something like this:
There is a number after 0.tcp.ngrok.io:15707. You need to remember this port number. Please keep this window on if you want to keep this tunnel open.
Then you can ssh to your remote server by copying the command: